Realme X3 SuperZoom launches with the Snapdragon 855+ and 120Hz display
Design-wise, the Realme X3 SuperZoom looks quite similar to the X50 5G, which launched in China at the beginning of the year. It features a similar-looking 6.6-inch Full HD+ display with an LCD panel and a high 120Hz refresh rate. The display is protected under Gorilla Glass 5. Since this is an LCD and not an OLED panel, the X3 SuperZoom features a side-mounted fingerprint scanner – also seen on the X50 5G as well as the Realme 6 and 6 Pro. Readmore...

LG Optimus G Pro (Unlocked)
LG F240S Optimus G Pro 4G LTE is a new and updated version of Optimus G smartphone and comes with notable enhancements in display, size and processor. It features a huge 5.5-inch True Full HD IPS Plus LCD that essentially makes it a phablet. Readmore..
Features Canon 650D and Nikon D5200 Which One is Best?
The beginner segment is always interesting to discuss, because the camera in this segment is still quite affordable but its already abundant and can be therefore people are no longer interested in buying a more expensive camera class. Readmore...
Review OPPO Find 5
In 2013 was the triumph of mobile phones with a screen resolution of Full HD TV rival. OPPO Find 5 is one of them, 5 inch screen includes a resolution of 1920x1080 pixels. This makes the screen OPPO Find 5 has a density of 441ppi, alias the same as the Sony Xperia Z and HTC Butterfly. Readmore...

9 Smartphone with Most Durable Battery in the World
9 Smartphone with Most Durable Battery in the World. In addition to its features, things we should consider when choosing smartphones are the specifications, one of which is the battery life. Smartphone useless we have a sophisticated but battery endurance for a while, we will be annoyed at having to often to charge our smartphones. Readmore...
HOW TO CHOOSE A SMARTPHONE WITH THE RIGHT PROCESSOR?
Tips for Choosing a Good Phone and As Needed
Here is a review of tips on how to choose a good cellphone that suits your needs.
When buying a new cell phone, be sure to know some tips so you don't choose the wrong one and get a quality product. So how do you choose it? Here's the review.
How to choose a new cellphone that suits your needs is actually not too difficult. Especially now that there are more and more smartphones available on the market, ranging from cheap to premium class that you can choose from. You only need to understand the needs of the cellphone you want to buy.
By choosing a smartphone that suits your needs, it will be easier for you to carry out various activities with this new smartphone,
see the following reviews of tips for choosing a good smartphone that suits your needs.
1. Adjust your budget
The first thing to consider when choosing a new cellphone is to make sure the budget you have matches the price of the gadget you want to buy.
You can adjust your financial capabilities to choose a new cellphone. If your budget is limited, then you can choose some cheap cell phones with large RAM, which are widely available on the market.
But if budget is not your main obstacle, then you can choose some of the latest cellphones that have the support of qualified specs and features so that once you use them you are very comfortable and support increased productivity.
2. Choose a cellphone from a well-known brand
Sometimes, some consumers choose smartphones from familiar brands that are well known to the public.
This is reasonable because as a layman, of course, you want to get a smartphone that is of high quality and easy to choose.
One example is Samsung, which has no doubt about its quality.
In addition, its after sales service is also qualified so that if the unit has a problem it can be easily brought to a service center which is easy to find and spread in almost all major cities in the country.
3. Check RAM Capacity
RAM is an important component that needs to be considered when choosing a good new HP.
To support optimal performance, you can choose a smartphone that has a large RAM capacity.
With the support of a large RAM capacity, smartphone performance is getting lighter, multitasking is getting smoother so you can download many of your favorite games or applications.
4. Select a Qualified Processor
Tips on how to choose a good and durable cellphone, then what needs to be considered is to choose a smartphone that has qualified processor support.
Apart from choosing a smartphone with large RAM, choose a fast processor so that the resulting performance is maximized and supports a variety of mobile activities that are more comfortable and efficient.
5. Battery Capacity
Pay attention to the battery capacity of the smartphone you want to buy. Because the latest smartphones are now increasingly sophisticated and have many applications, of course, require large power consumption, therefore you can choose a smartphone that has a large battery capacity.
Choosing a cellphone with large battery support has many advantages, including being able to play games longer, being able to stream your favorite movies all day and not having to worry about running out of power when traveling or leaving the house so you don't need a power bank which is quite complicated when you leave the house.
We hope that the tips on how to choose a cell phone that is good and according to your needs above will be useful for you so that you can get a quality smartphone and get a cell phone that fits the needs you need at this time.
Source from HERE
Come on, Get to Know Chipset Functions in Smartphones & Their Types!
In the mobile industry, the roles of processors and graphics processors are inseparable. Things are different if you look at the world of PCs, the main processor or CPU and graphics processing processor or GPU generally exist separately. Even then technology allows a PC processor to have an integrated graphics processor.
The CPU and GPU are generally united in a circuit board ( motherboard ) in which there is what is called a system-on-chip or SoC. However, the term SoC is less popular. Most people refer to it as a chipset only.
This chipset functions to manage various computing tasks and connect various hardware on the motherboard.
In the mobile industry, the chipset has a role more than just connecting the CPU, GPU, memory and others. The chipset is a piece of hardware in which there are various components to manage data processing, graphics processing, camera processing (ISP), modem, and others.
In a way, the chipset is a complete package that is the main "brain" behind the capabilities of a cellphone. All the features presented by a cellphone must be supported by the chipset itself. If a cellphone supports 2K screen resolution but the chipset used only supports full HD, obviously this can't be done.
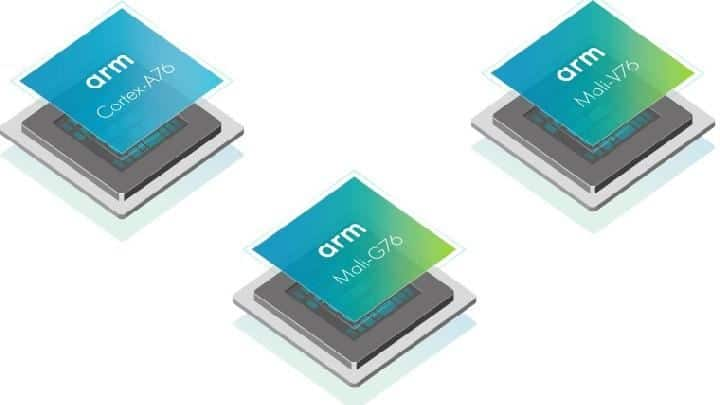
ARM Chipset and Architecture

Inside the chipset of a mobile device , there are controllers for video, audio, screen display, type of RAM used, modem (for internet needs), and other new features. Examples include fast battery charging support features or features to maximize AI.
Interestingly, the size of the chipset is small but there are many functions in it. Imagine that with a small form factor, there is plenty of space for the CPU, GPU, modem control, ISP ( Image Signal Processor ), NSP and others. This is of course possible because the chipset is not just built but through a fabrication process and based on a certain architecture.
To imagine how the position of each component is in the chipset, you can see in the image below.

The image above is the architecture of a chipset or system-on-chip (SoC). As can be seen in the picture, in such a small size, the chipset maker or designer is able to include all the functions that make it the "small brain" of a smart device called a smartphone.
From that explanation, it's clear that the chipset is a "core package" that concerns everything. In a way, the chipset is not just the CPU and GPU, but a regulator to produce good images, a place to process to get a good internet signal, rely on RAM, and other functions.
So, how can a small hardware can have various functions to run a device? Thanks to ARM Holdings , the company that designed the ARM processor architecture.
For information, a processor for a device was born from the architecture that was made. There are two types of processor architecture. There is a RISC (Reduced Instruction Set Computer) type and secondly there is a CISC (Complex Instruction Set Architecture) type.
A simple explanation of the differences between the two architectures is in the type of instructions and their use. RISC is a type of processor architecture with simple instructions but is able to offer good performance and save power.
While CISC is a type of processor architecture with more complicated instructions. However, CISC is able to offer faster performance even though it is more power intensive. Because of that CISC is used as the basis for the x86 architecture which is then used for complex computations such as processors from AMD and Intel.
Meanwhile, RISC is an instruction set for more specific computing tasks. This ARM architecture was present in the 80s for light computing. When the mobile industry skyrocketed, ARM architecture processors were widely used. In fact, almost all mobile devices use the ARM architecture.
Thanks to the popularity of the use of mobile devices, of course, the name ARM Holdings as the designer of the ARM architecture has become more successful. It's just that you need to know that ARM Holding has a different business system from Intel and AMD.
Intel and AMD carry out processor production starting from designing, producing, to selling the processor itself. While ARM Holdings only design it. This design is sold to other companies through the purchase of a license. Samsung, Qualcomm, Apple and others all manufacture chipsets with design licenses from ARM.
The architectural design made by ARM itself consists of a processor design called Cortex and a GPU called Mali. Later this design was bought by another manufacturer. These manufacturers are what we call chipset manufacturers.
Smartphone Chipset Manufacturers
Chipset manufacturers who buy ARM architecture licenses then create their own chipsets. As stated on the Jagatreview.com site , these manufacturers can choose 2 types of licenses provided by ARM.
The first license provided by ARM is to use a processor design that has been designed by ARM. If there is a chipset that uses a processor with the name Cortex and GPU Mali, this means that the chipset manufacturer chose to use an ARM processor design.
The second license is a license for custom-core. This license allows manufacturers to redesign their processors so that they are compatible with the ARM architecture. The characteristics of this chipset manufacturer can be seen from the names of the processors and graphics processors that do not use the names Cortex and Mali.
So, who are the chipset manufacturers for smartphones or other mobile devices ? The answer is, there are about 5 major manufacturers that all five have ARM architecture license permits. Generally these five manufacturers only design a chipset based on an ARM license. The production process is usually handed over to other parties, namely semiconductor companies such as TMSC or Samsung Semiconductor.
Many chipset manufacturers make smartphones with various types of chipsets. What are these types? Check out the discussion below.
Types of Chipsets Used in Smartphones
So, after discussing the chipset architecture and its manufacturers, now let's get to know the types of chipsets that are most commonly used on cellphones.
1. Qualcomm Snapdragon

Snapdragon is the most famous chipset. This chipset was developed by Qualcomm, an American company that has recently focused on presenting chipsets for various platforms. Qualcomm itself has license permission to design processors from ARM.
Due to the license permit, there are several Snapdragon chipsets that do not use Cortex processors. This is because Qualcomm developed its processor under the name Kryo. In addition, the graphics processor or GPU on Snapdragon is not Mali but Adreno.
Adreno was originally owned by ATI Radeon under the name Imageon. In 2006, ATI Radeon was purchased by AMD. This acquisition caused Imageon, a development project for mobile graphics processors to be abandoned. In 2009, Qualcomm bought Imageon from ATI (which was already owned by AMD) and changed it to Adreno, an anagram of Radeon.
This combination of Kryo processors and Adreno graphics is mostly found in high-end and middle-class Qualcomm chipsets. Call it Qualcomm Snapdragon 865, 888, 870, 855 and 855+, Snapdragon 845, and others. Snapdragon itself is the chipset that users like the most, it's no wonder that many mobile phone vendors choose Snapdragon as the best choice chipset.
2. Apple A (Fusion,Bionic)

Similar to Qualcomm, Apple has a license to develop its own processor based on the ARM architecture. Apple developed their chipsets with the simple name of the A series which was then followed by letters like A7, A8, A9, and so on.
Since the A10 series, Apple has added additional names behind their chipset series. For example, the A10 has the official name Apple A10 Fusion. Next is the A11 with the name A11 Bionic.
The name Bionic was maintained when Apple released its next generation of chipsets, up to A14 Bionic. The Apple A14 Bionic is the brain alias chipset in the Apple iPhone 12 Series .
Similar to the operating system and their exclusive products, the chipset developed by Apple is also available exclusively for Apple devices, not only for smartphones, of course. An example is the Apple A12 Bionic variant, namely the A12X Bionic which is used as the "brain" of the third generation iPad Pro 11-inch and iPad Pro 12.9.
3. MediaTek

MediaTek is one of the biggest chipset manufacturers. This Taiwanese company consistently delivers chipsets with high features but at an affordable price. At first, MediaTek was known as a less than good chipset manufacturer. Many consider cellphones with chipsets from MediaTek to often heat up quickly and their performance is not fast enough.
MediaTek is also improving and presenting several good chipsets such as the Helio G series type for gaming and Dimensity which focus on performance and 5G network support. In the middle class and low price class, there are also many Mediatek chipsets that are okay. Many local cellphone vendors also use MediaTek as a chipset because the production costs are cheaper.
MediaTek has a processor called Cortex but for the GPU, sometimes they use Mali, sometimes they also use PowerVR. It could be that MediaTek has a semi-custom ARM license that allows manufacturers to develop certain parts of a chipset.
4. Samsung Eyxnos

Apart from being known as a well-known mobile phone manufacturer, Samsung is also known as a chipset manufacturer. Samsung develops its own chipset under the Exynos name. This chipset is not inferior in performance when compared to Snapdragon, even its performance tends to compete.
The Exynos chipset itself is widely used in cellphones made by Samsung. But not only Samsung, other manufacturers such as Vivo have smartphones with the Exynos chipset. Meizu, another manufacturer from China, has several cellphone products that use the Exynos chipset.
Exynos itself consists of a Cortex processor and a Mali GPU. It's rare for Samsung to change these two parts. I don't know which license Samsung uses, but Exynos comes as a good chipset. For example the Exynos 2100 which is used on the Samsung Galaxy S21 series device. In the future, the Exynos chipset will use a GPU from AMD Radeon which will be used in high-end Samsung phones in 2022.
5. HiSilicon Kirin (Huawei)

Through a subsidiary called HiSilicon, Huawei develops their own chipset. The chipset made by Huawei is named Kirin which comes from the ARM architecture. This Kirin chipset is specifically made for cellphones made by Huawei and Honor, a sub-brand from Huawei.
At first, the Kirin chipset was not taken into account, considering that Huawei phones with Kirin rarely get the spotlight. Only when Huawei released the Huawei P20 Pro which was equipped with Kirin 970, Kirin was considered a capable chipset. Huawei also presented its successors, namely the Kirin 980 and Kirin 990 5G, and the Kirin 9000 5G, which has faster performance.
Unfortunately, the development of the Kirin chipset and its production have been constrained. This is due to the ban on the use of American technology for Huawei because it is considered to have tools for spying. This ban has an impact on Huawei's business line on mobile devices, especially Android.
6. Unisoc

Recently, Realme has also started using Unisoc chipsets through the C11 2021 realm product. It is possible that in the future many brands will use Unisoc chipsets. Moreover, Unisoc began to improve by presenting a chipset with a smaller fabrication. An example is the Unisoc Tiger T618 which has a 12 nm fabrication and is used in the Advan GX
The Unisoc chipset itself used to be known as Spreadtrum. Spreadtrum is a chipset manufacturer which was later acquired by Tsinghua Unigroup. Tsinghua Unigroup then acquired a company called RDA Microelectronics.
For your information, RDA Microelectronics is a semiconductor company that designs, develops, and markets radio-frequency-system-frequency semiconductor products for cellular, connectivity, and broadcast applications.
In 2018, Spreadtrum and RDA Microelectronics merged and rebranded under the name Unisoc. This Unisoc then presents a 5G chipset with a 6nm fabrication called the Unisoc T7520.
7. Nvidia Tegra
Graphics card manufacturers for PCs, Nvidia, are also playing in the mobile realm. This company presents an ARM architecture chipset with the Nvidia Tegra name. Nvidia Tegra is presented as a chipset for mobile devices that focus on gaming.
Unfortunately, Nvidia seems less focused on the mobile industry . This company is more focused on developing graphics card products for computers. This certainly has an effect on Nvidia Tegra, which is rarely looked at by cellphone or tablet manufacturers.
8. Other Chipset Manufacturers

Apart from the seven names mentioned earlier, many other companies also produce chipsets. Generally the companies are small and focused on a specific device. Like Rockchip, which produces chipsets for TV Box devices.
Intel, a giant company in the realm of PCs, has also presented a chipset for mobile. This company was once the brains behind the first generation of Asus Zenfone phones. Unfortunately, Intel raised the white flag and returned to the realm of x86 architecture processors.
Intel's surrender is because Intel processors for mobile devices are not developing. The issue of overheating processors and limited game support on Android is reportedly one of the reasons Intel processors for mobile were not continued.
Conclusion
Actually, many other companies also want to try to produce their own chipsets. Xiaomi has tried to produce its own chipset with Surge, it's a shame it wasn't developed. Business focus is certainly a concern too.
Therefore, now and in the future, chipsets in smartphones will still be controlled by the big 5 players (order 1 to 5). And whoever controls the market, ARM, as the design licensee, will always be the winner.
source from : https://carisinyal.com/chipset-smartphone/
Realme X3 SuperZoom launches with the Snapdragon 855+ and 120Hz display

Price & Availability
Realme X3 SuperZoom Specifications
| Specifications | Realme X3 SuperZoom |
|---|---|
| Dimensions & Weight |
|
| Display |
|
| SoC |
|
| RAM & Storage |
|
| Storage Type | UFS 3.0 + Turbo Write + Host Performance Booster (HPB) |
| Battery |
|
| Fingerprint Sensor | Side-mounted fingerprint |
| Rear Cameras |
|
| Front Cameras |
|
| Android Version | Realme UI based on Android 10 |